CIO, CTO, CSO, IT Service Management, IT Job Description, Sarbanes Oxley, and IT Salary News
CIO - CTO - CSO News
CIO Management Tool Kit
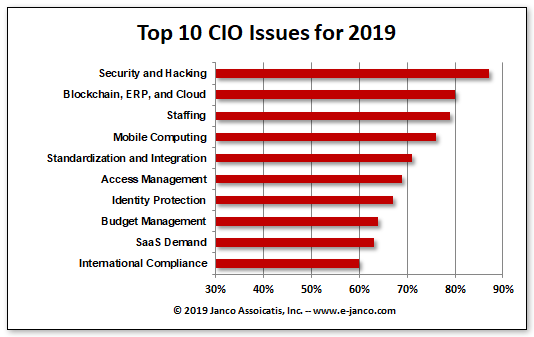
CIO management concerns are constantly changing
CIOs and CTOs are in a constantly evolving field, however world class CIOs and CTOs focus on three areas to help them manage more effectively. They are:
- Technology
- People
- Infrastructure
Massachusetts and New York mandated security requirmements
Meaningful Security Compliance
 The Massachusetts mandated security is much less extensive than the New York Cybersecurity law. There currently is an increased focus on data. Now CSO need to set how data is categorized, stored, governed, secured, and reported as firms strive to avoid data breaches. Companies need a CSO who owns the security practice and programs. Additionally, companies need an individual who owns data at an enterprise level (chief data officer see https://goo.gl/eTCkvB) to ensure effective data governance. The CDO and CSO together work to avoid data breaches, detect when breaches do happen, fix the situation effectively, and quickly report breaches in a way that complies with each states regulations.
The Massachusetts mandated security is much less extensive than the New York Cybersecurity law. There currently is an increased focus on data. Now CSO need to set how data is categorized, stored, governed, secured, and reported as firms strive to avoid data breaches. Companies need a CSO who owns the security practice and programs. Additionally, companies need an individual who owns data at an enterprise level (chief data officer see https://goo.gl/eTCkvB) to ensure effective data governance. The CDO and CSO together work to avoid data breaches, detect when breaches do happen, fix the situation effectively, and quickly report breaches in a way that complies with each states regulations.
Effective Managers Defined
Effective Managers is what every CIO is looking for
 Effective managers are analytical leaders who are adaptable and possess systematic and methodological ways to achieve results. It may sound corny but they apply the scientific method that involves formulating hypothesis and testing to prove or disprove them.
Effective managers are analytical leaders who are adaptable and possess systematic and methodological ways to achieve results. It may sound corny but they apply the scientific method that involves formulating hypothesis and testing to prove or disprove them.
A scarce resource in many organizations is human ability and competence. That is why organizations need to develop every employee for growth in these skills. But having sound competencies is not enough. Key personal qualities complete the package of an effective leader.
- more info
Top 10 Reasons Why Telecommuting makes sense
Telecommuting makes great economic sense
 Telecommuting Top 10 Reasons Why
Telecommuting Top 10 Reasons Why
- Flexible Work Hours
- Reduced costs
- Ease the strain on employees
- More Productive
- Minimize Non-Work Distractions
- Better Morale
- Green Solution
- Staying Healthy
- Potential Tax Deductions for ewmployees
- Reduce the Need for Outsourcing








